Making sure that your own domain name portfolio has layers of security is a recognised fundamental, that is within your control and ensures that the portfolio is constantly monitored and necessary updates are made. However, do you check if companies in your supply chain are taking the same precautions? In the last year we have seen an increase in high profile breaches for large organizations, some of which has been due to vendors that were breached.
In the recent Domain Security report published by CSC, we highlight some of the key components that the Global 2000 and top 100 unicorns have in place to mitigate risks around their domain names. What we saw in the results is that the top 100 unicorns in many aspects did have better coverage of domain name security components.
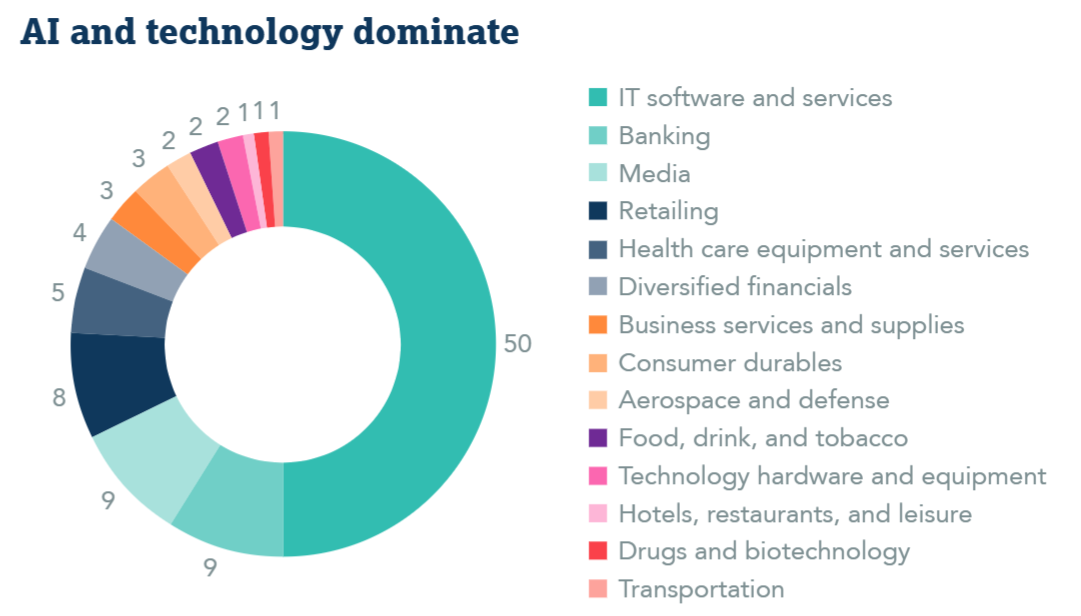
Over 50% of the Top 100 unicorns are in the technology sector and are more than likely within the supply chains of the Global 2000 companies. In comparison with the Global 2000 across 8 domain security attributes, unicorns have a higher scoring in 5 categories. Even though they score higher than the Global 2000, adoption of some attributes is still very low.
The key areas where they are stronger are:
- Email security with higher adoption of SPF, DKIM and DMARC.
- DNSSEC 16% adoption vs 10%
- CAA records had 33% adoption vs 11%
What all of these have in common is that they are managed through DNS records, this suggests that teams managing the domain names for unicorns are likely IT professionals with good knowledge of security protocols available in DNS without incurring much costs for the company. Also, these companies which are by nature newer probably have a less complex set up, which makes it easier for them than for the large global organisations.
Governmental interventions
In the EU we saw the introduction of the NIS2 directive which in a nutshell is GDPR for technology. In this directive it outlines how you should be adopting redundancy where possible and setting up checks on your supply chains. At present many countries are bringing this into local law. We are also seeing other governments around the world looking at adopting similar rules. This is all to make companies in critical industries more resilient against all different kinds of attacks that now are seen on a regular basis.
What should companies be doing?
In short, security surveys should be part of your approach to vendors who provide technology as part of your supply chain. While such surveys are likely in place, you must ensure that you don’t overlook how they protect their domains and DNS. Some of the critical questions should be:
- What is your guaranteed uptime for DNS services?
- Please document your track records for the past 10 years
- Do you offer SOC II reporting?
- Do you use an enterprise-class registrar for your critical domains?
- Are your critical domains locked at the registries and registrars?
- Do your critical domains have DNSSEC-enabled?
- What email authentication protocols are used on your critical domains?
- Do you enforce policies on authorized certificate authorities for SSL certificates used?
- Do you proactively monitor your critical domains for fraudulent third-party lookalike domains?
By asking these questions, you can quickly ascertain whether the providers are treating domain name security as seriously as you are. Domain security is still the missing element in a lot of companies’ security posture, the more you can educate internally and through suppliers, the greater the chance of reducing risks that can severely damage your brand.
Read the full report
Download the 2026 Domain Security Report to see key domain name security components used by the Global 2000 and top 100 unicorns, and where adoption is still low.
