By Letitia Thian, Marketing manager APAC Share this post



David Conrad, CTO of The Internet Corporation for Assigned Names and Numbers (ICANN), recently presented a keynote during a webinar we collaborated on with other internet organizations. Below is a summary of his explanation of the domain name system (DNS) ecosystem, its vulnerabilities, and threat mitigations.
The internet as we know it largely depends on DNS. It is akin to the telephone book of the internet, translating domain names into IP address, so users can easily look for websites with names instead of a string of numbers. The DNS isn’t a single entity, and comprises the protocol, namespace, and service; its ecosystem extends to include software, provisioning, and others.
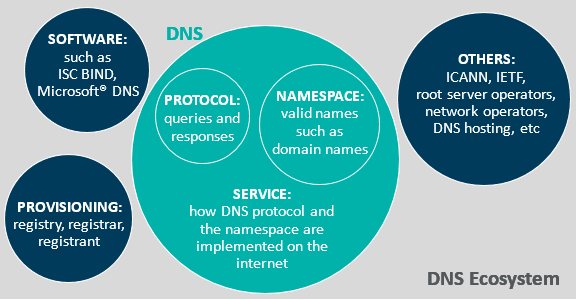
The DNS protocol, invented in 1983, was intended to be lightweight with a simple query response behavior. To allow the DNS to scale, it was designed with a tree-like structure; each branch and level of domains, such as top-level domains, can be independently administered. With an expanding structure and multiple segments in the DNS ecosystem—software, registries, network operators, hosting providers and more—the DNS’ complexity adds to the challenge in security.
David shared that “the DNS is a critical component of the internet, and the DNS ecosystem is large, complex, and has myriad players of varying levels of competence, resulting in a (very) large attack surface.”
When the DNS was first developed and defined, with no protection against data corruption, security wasn’t a focus. Below are some of the DNS ecosystem vulnerabilities and their mitigations.
| Attacks on the | Type of attack | Mitigation |
DNS protocol | DNS cache poisoning Privacy compromise | DNS security extensions (DNSSEC) DNS-over-HTTPS and DNS-over-TLS digital certificates |
DNS namespace | Homogylphs (ҫscdbs.com) and typosquatting (cssdbs.com) | Interfaces that make international domain names (IDNs) and unsecured sites more apparent, and end-user vigilance |
DNS service | DNS hijacking Distributed denial of services (DDoS) | DNSSEC DDoS mitigation services |
| Registrar or registrant | Account breached to modify domain data | Registry and registrar lock |
We have seen recent incidences compromising the DNS on various fronts:
- MyEtherWallet.com
An attack on the DNS protocol and service through a combination of routing system attack and DNS cache poisoning redirected users to a site in Russia and U.S. $150K was stolen.
- COVID 19-related attacks
Attacks on the DNS namespace, with a spike in domain registrations, where a small percentage of COVID-19 related names were primarily used for phishing, malware distribution, and spam, with the vast majority apparently being parked names.
- DNSpionage and Sea Turtle
Attacks on DNS provisioning and the namespace, where top-level domain registries and registrars were compromised, most likely due to unpatched systems.
The DNS provides a ubiquitous service critical to the function of the internet. This, combined with the large attack surface, make the DNS ecosystem an excellent (and frequent) target of attack. It’s constantly evolving to improve its efficiency, security, and function, such as DNSSEC. But each part of the DNS and its larger ecosystem has its own set of vulnerabilities, from bugs within the DNS protocol itself to how the DNS is deployed for operation. Hence, fixes for those vulnerabilities requires participation of all actors within the ecosystem—from registrants to registries, DNS operators to software developers, end users to governments—to play a role in ensuring the security of DNS and the internet.
To listen to the full explanation and details by David Conrad, watch the recorded webinar here. >>