Unsuspecting website visitors are often unaware when they have landed on a spoofed page or are re-directed to malware-hosting web servers designed to steal their sensitive data and information. This attack is known as subdomain hijacking, or subdomain takeover. A web user’s private information is then traded on the dark web and cybercriminals profit, further fueling the expansion of identity theft in the online world.
In a space shrouded by anonymity by design, the brands and organizations targeted may not be directly compromised, however, they likely forgot about domain name system (DNS) records that were left behind or misconfigured, leaving their customers open to theft. In the past, this has been known as a lame delegation or dangling DNS. Cybercriminals monitor the internet for publicly available information, including DNS zone records, that point to destinations no longer used by a brand. By hosting content on cloud providers who don’t run verification checks, criminals can request a previously used zone destination and start to again receive web users landing on these subdomains loaded with their own illegitimate content, all without infiltrating an organization’s infrastructure or third-party service account. Aside from reputation damage and loss in consumer confidence, the fraudulent web pages and associated emails could be used in phishing campaigns and malware distribution, leading to more damaging data and security breaches.
What is a subdomain hijack?
A subdomain hijack is a cyber threat where an attacker gains control of a legitimate subdomain that’s no longer in use to host their own fraudulent or malicious content. They can do this by cleverly exploiting forgotten DNS records to point to their own content.
Video
A result of poor housekeeping
Subdomain hijacking is a result of poor housekeeping or life cycle management of DNS records. DNS records housekeeping is one of the worst managed tasks in business due to 20 plus years of history with different owners, policies, and vendors.
Companies promptly take down websites with a paid hosting provider when a brand is retired or a campaign is no longer running, but sometimes leave the associated DNS records intact. Over time, there’s an accumulation of DNS records that become unaccounted for. Administrators, unaware of its history, hesitate to delete these legacy records fearing they may be tied to critical infrastructure that will inadvertently bring down operations.
One in five DNS records point to content that does not resolve
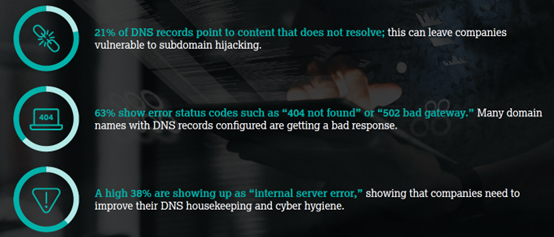
In our latest report, we analyzed over six million DNS records from our database and further filtered the set to just over 440,000 DNS records by looking at A records and CNAMEs pointing to cloud infrastructure where there is potential for compromise by subdomain hijacking. We found that many companies are susceptible to subdomain hijacking.
We further observed a trend where companies with large portfolios may not have centralized management of their cloud providers, making it a challenge for them to have good oversight into all their DNS records.
Read more: Subdomain Hijacking Vulnerabilities Report
Adhering to cyber hygiene
Organizations could have decentralized management, staff turnover, and extensive web properties. Without proper oversight of digital records and administration, organizations accumulate “noise” that makes it difficult for them to maintain good cyber hygiene, resulting in easy exploits for cybercriminals.
At CSC, we recognize these challenges, and the threat a subdomain hijack could pose for companies. Additionally, subdomain hijacking is one of many domain security threats that exists today, including domain and DNS hijacking, domain shadowing, and cache poisoning. These threats often serve as enabling attacks to launch more egregious phishing and ransomware attacks, along with business email compromise (BEC), email spoofing, or even data breaches.
We recommend all companies adopt a subdomain monitoring solution that not only alerts you when changes to your DNS records are detected, but also provides you context so you can make informed decisions and take appropriate action to prevent a subdomain hijack.
Contact us to learn more about our Subdomain Monitoring solution. >>