What is a DDoS attack?
In a distributed denial-of-service attack, a bad actor overwhelms a network, service, or application with unusually high volumes of traffic, which effectively blocks requests from legitimate users. Exploited systems can include computers, networked resources, and Internet of Things (IoT) devices like smart speakers and wearable devices. In recent years, these types of cyber attacks have been increasing in frequency, scale, and complexity.
Are DDoS attacks illegal?
Yes, DDoS attacks are cybercrimes that have caused millions of dollars of damage. For example, in the United States, hackers and other individuals have been charged with federal criminal offenses for carrying them out. Many other countries have similar laws.
A website may become overloaded by a genuine spike in customer traffic, such as on a major shopping holiday, driving the hosting environment or site to slow down or crash. However, a premeditated disruption caused by a network of hijacked devices is a crime.
How do DDoS attacks work?
A denial-of-service (DoS) attack uses only one online connection to overwhelm a machine or network, but a distributed denial-of-service (DDoS) attack harnesses multiple infected machines, called botnets, to flood the victim’s infrastructure, potentially causing catastrophic failure. Cybercriminals take control of these botnets using malware (malicious software) and command them to bombard the target with massive amounts of network traffic, often in the form of malicious packets. Since DDoS attacks distribute the load across many compromised devices, they are much harder to mitigate than standard DoS attacks.
At a technical level, packets are the fundamental units of data that travel across the internet. Every interaction—such as loading a webpage, streaming a video, or sending an email—relies on packets being transmitted between servers and users. In a DDoS attack, the botnets generate an overwhelming flood of packets, exhausting the target’s bandwidth, processing power, or connection limits, effectively crippling online services.
While domain names themselves are not typically the direct target of DDoS attacks, they can be severely impacted when domain name system (DNS) servers or supporting infrastructure are attacked. A distributed denial-of-service event that renders a domain unreachable can disrupt business operations, block customer access, and damage a company’s reputation.
Types of DDoS attacks
Although there are a larger number of different types of distributed denial-of-service incidents, most can be grouped into these general attack types.
Application layer attacks, sometimes called Layer 7 attacks, target the highest layer of the Open Systems Interconnection (OSI) model, where user interactions with applications take place. This layer handles tasks such as loading web pages and managing database queries. Attackers flood an application with an overwhelming number of seemingly legitimate requests, generating excessive network traffic that exhaust server resources and cause service disruptions.
Protocol attacks, sometimes referred to as state-exhaustion attacks, exploit vulnerabilities in communication protocols at the transport and network layers (Layers 3 and 4 of the OSI model). These attacks aim to consume finite resources such as memory or connection state tables in firewalls, load balancers, or servers. Some involve sending malformed or strategically crafted packets that take advantage of how a system processes network traffic, while others manipulate connection handling to create bottlenecks. Because protocol attacks do not always require deep technical knowledge, they are relatively common.
Volumetric attacks, also known as network-based attacks, are the most prevalent and best known type of DDoS attack and focus on overwhelming a target’s available bandwidth. These attacks involve flooding the target with massive amounts of requests, often using reflection and amplification techniques to magnify the traffic volume. One example is DNS amplification, where an attacker exploits open DNS resolvers by sending small spoofed queries that generate much larger response packets directed at the victim’s IP address. The sheer volume of these responses saturates the network, making it difficult for legitimate traffic to pass through.
A cybercriminal may use any combination of these methods to form a multi-vector assault, increasing the complexity and severity of the assault by targeting different layers simultaneously.
Learn more about stopping DNS amplification activity—and more—from our insight paper, “Six Ways to Strengthen DNS Security.”
Consequences of DDoS attacks
In today’s constantly online world, an organization may suffer from even a brief period of unplanned downtime. In the immediate aftermath, a business may expect to lose revenue from customers, productivity from employees, and potential costs from resolving security vulnerabilities.
A significant incident may result in longer-term repercussions, such as brand tarnishing, loss of customer trust, exposure of other security flaws to adversaries, and legal liability if the company is found to have failed to take adequate measures in preventing the DDoS incident.
Enterprise DDoS protection
Distributed denial-of-service attacks are both easy and inexpensive to carry out, making them increasingly common against DNS systems to disrupt online businesses. Because DNS translates domain names into IP addresses, it’s a critical target, and proper cybersecurity measures must be taken.
How to stop a DDoS attack
Strong preventative measures are critical in quickly detecting and stopping a DDoS attack with minimal to no impacts on day-to-day operations.
To defend against DNS-based attacks, we recommend using a solution with multiple layers of DDoS protection. DNS nodes—key components that handle domain name resolution—should include DDoS mitigation equipment to constantly monitor for unusual traffic patterns, such as malformed traffic or high traffic from suspicious locations. Early detection is key.
Most distributed denial-of-service attacks are smaller in scale and can often be mitigated without major disruption. Techniques such as rate limiting and traffic filtering help manage these attacks by controlling request volumes and blocking malicious traffic.
For large-scale surges, malicious traffic should be automatically rerouted to a separate, purpose-built network capable of handling the load, a measure known as DNS redundancy. This isolates potential damage to the targeted DNS infrastructure. With the threat contained, a 24x7 security operations team is free to respond more effectively.
How to prevent DDoS attacks
Reducing your organization’s overall attack surface would give cybercriminals fewer opportunities and help prevent DDoS attacks. To enhance your defenses, consider following these best practices:
Reinforce security for interdependent services, such as DNS and cloud providers
Minimize connection with IoT devices to limit potential exposure
Implement security measures for remote employees, as multiple Wi-Fi connections increase the attack surface
Use a security platform that offers comprehensive oversight of your domain portfolio, helping identify and mitigate potential security blind spots
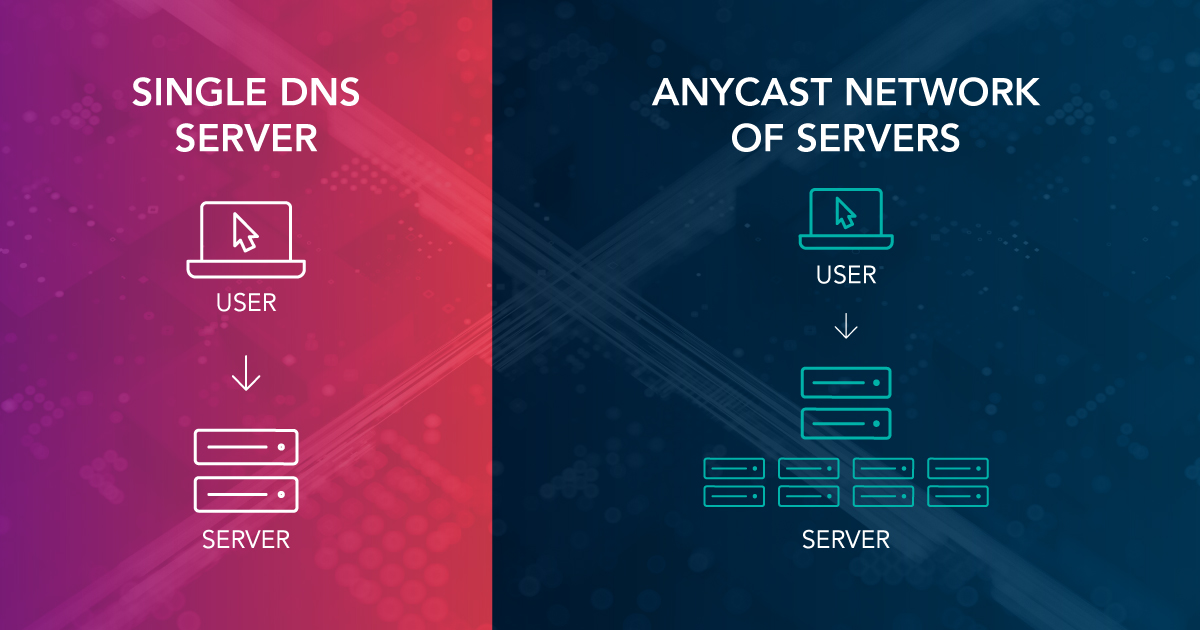
Leverage DNS redundancy by using a network with multiple primary and backup nodes across the globe for reliable coverage
Use built-in DDoS protection and DNS security extensions (DNSSEC) to guard against unwanted traffic and other DNS-based attacks
Partner with a security provider that offers services like DDoS scrubbing centers that filter and remove malicious traffic before it reaches your network
Defend your DNS from DDoS attacks
Plan ahead and protect your business by ensuring your DNS remains resilient against distributed denial-of-service threats. Our enterprise-class DNS services, powered by Vercara, combine Anycast routing, built-in DDoS mitigation, and global redundancy to maintain uptime and prevent service disruptions. With continuous monitoring and automated alerts, our solution helps identify vulnerabilities and detect potential threats before they impact your business.
Frequently asked questions (FAQ)
A distributed denial-of-service attack overwhelms a website, server, or network with excessive traffic, disrupting normal operations and making online services unavailable to legitimate users.
DDoS attacks are illegal in most countries and can result in severe penalties, including fines and criminal charges. Many jurisdictions classify them as cybercrimes under laws that prohibit unauthorized interference with computer systems.
Signs of a DDoS attack include a sudden spike in traffic, slow website performance, unexpected outages, and an inability to access online services. Security monitoring tools can help detect unusual traffic patterns associated with an attack.
Yes, businesses can mitigate DDoS attacks using rate limiting, traffic filtering, and DDoS mitigation services that detect and block malicious traffic before it reaches critical infrastructure. Implementing DNS redundancy also helps by distributing DNS queries across multiple networks, reducing the risk of a single point of failure during an attack.
A successful DDoS attack can disrupt business operations, impact revenue, and damage brand reputation. Enterprises should have a mitigation plan in place, including DDoS protection services, network redundancy, and incident response strategies.
Related resources
Monitoring Marketplaces:
Image AI Available Now to Identify Brand Threats
6 Ways to Strengthen DNS Security
Domain Security Checklist
Make an inquiry
All fields marked with * are required.